
Developer: LuGus Studios
Publisher: Iceberg Interactive, VAF
Platform: PC
Tested on: PC
Midnight Protocol – Review
Have you ever wanted to be a hacker? No, we’re not talking about guessing a friend’s Facebook password and leaving a funny message on their timeline, but actually infiltrating a network, snatching sensitive information or valuables, and disappearing again without a trace. If the answer is yes, then Midnight Protocol might be just up your alley. You might not be actually performing illegal or morally questionable activities, but the game sure as hell makes you feel like you are. The question, of course, is whether simply emulating the feeling of being a hacker is enough to make Midnight Protocol a game worth playing. Read on to find out.
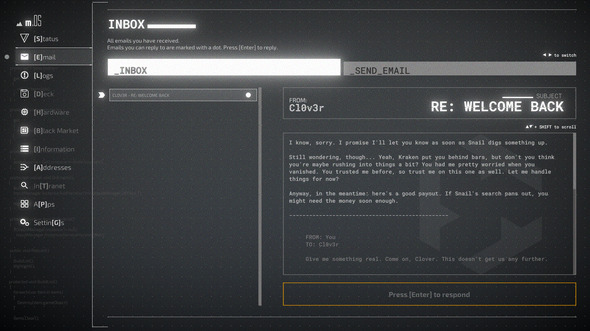
Story
Midnight Protocol’s story, which is told mostly through email messages, puts players in the role of Data. Part of a collective of hacktivists, Data makes his return to the hacking scene after needing to lay low for a while. The last time Data was active, his doxxing actions put the authorities on his trail, and even now Data’s crew fears that his return is too soon. Even so, our hacker protagonist feels the need to take down corporations that don’t have the public’s best interest in mind, and soon enough he’s taking on contracts again. This time, however, Data may have bitten off more than he could chew, as cryptic messages randomly start to appear while he is hacking. We’re not going to delve into spoiler territory, but rest assured that while Midnight Protocol isn’t ashamed to stick to the cliché image of a hacker, the story arc itself takes a few surprising twists and turns.
Graphics
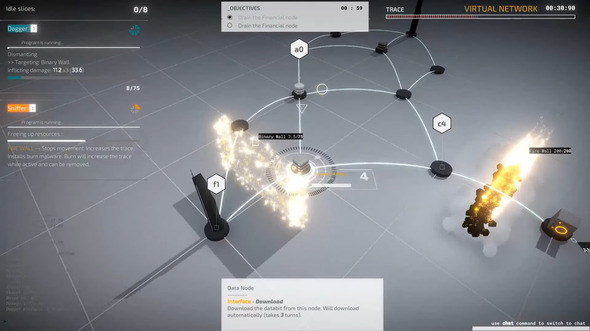
In order to drive the idea that you’re a hacker, Midnight Protocol’s visuals resemble a custom OS. This makes perfect sense, and the game looks fantastic for what it’s supposed to be. Those that like their games with a bit more flair can add various screen distortion effects but these are fully optional. Overall, the custom OS interface looks convincing enough, and because the game can be played in full-screen mode rather than windowed -which we highly recommend- a high degree of immersion is attained. Of course, some creative liberties were taken with how the missions are represented visually -in real life, there aren’t actual visual firewalls, and hacking is done mostly on a screen that only displays text (or so we assume) but what’s present here is effective, if not a little dramatic. Of course, given that this is a custom OS, creative liberties are perfectly acceptable.
Sound
We’re not quite sure how we feel about Midnight Protocol’s soundscape. You can enable the sound of keyboard typing while playing, but we wonder what the point of this option is if you can hear your actual keyboard while playing. Likewise, the game’s techno soundtrack sounds appropriate for the setting, as it sounds like something you’d expect to hear in a movie or tv show about hackers, but the game having an OST in the first place feels out of place as it’s supposed to be set inside a real computer. This is one of the few cases where not having music would’ve been more appropriate. Of course, you can simply mute the music in the game’s settings and go for full-on realism if you really want to feel like you’re a hacker. Just remember to turn off all the lights and wear a black hoodie as well while playing. The game’s OS sound effects are fitting and probably the best part about the game’s audio.
Gameplay
Midnight Protocol essentially combines puzzle gameplay with turn-based strategy and even some RPG elements, resulting in a title that feels unique without making the player feel alienated. Developer LuGus Studios put a spin on Midnight Protocol’s turn-based strategy gameplay by making it playable with only your keyboard. Your mouse isn’t even visible on screen, and every action you take is done by typing in commands. This mechanic really helps a lot with creating the feeling that you are a hacker. The idea that you’re supposed to type your way through a game using commands might be intimidating for those that have little experience with programming, but the game does a good job of easing the player into the mechanics.
After playing through the opening stages, Midnight Protocol’s controls felt logical and surprisingly natural as a result. The game’s main objective is of course to hack your way into the heart of your enemy’s mainframe, which is done by playing through the main story, but there are plenty of side missions that allow you to earn more credits. We’re not going to delve too much into the game’s mechanics here -all you need to know is that missions involve going into a target’s computer, where you must steal credits, gather data, or plant trojans. While doing this, you’ll need to avoid being detected and you are also confronted with firewalls, malware that drains your own resources, and other hindrances.
You have hacking tools at your disposal of course, including a cloaking program that makes you harder to detect, aggressive programs that let you brute force your way through enemy defenses, and leeching programs that steal credits automatically. Credits are used to acquire more powerful hacking tools, which then allow you to play more efficiently. The game’s missions are turn-based, so while you technically don’t have to worry about how long it takes you to complete a mission, time does factor into the rating you receive upon mission completion.
You only have a limited number of ‘slices’ at your disposal and you’ll need to assign these to your programs. The amount of slices you put into a single program determines its effectiveness: running multiple programs simultaneously means that individual programs take longer to complete certain tasks. This brings us to one of the few gripes we had with the gameplay. You only have a limited number of available actions each turn, but there were times where we had to “waste” a turn simply because we had to wait for a program to complete its task. Not using actions simply because we had nothing to do felt like a waste and disrupted the gameplay flow.
This was something that was especially frustrating early on, as there was only so much we could do, and luckily this became less of an issue later on. The game’s missions become increasingly difficult of course, but they never feel unfair or frustrating. Every time we failed one, it was on us, and more often than not, failure was a learning experience. Soon enough we memorized the pitfalls of a mission and were able to hack our way around it.
There is also a morality system present in Midnight Protocol, though it’s not as straightforward as the rest of the game. Taking certain actions will earn you ‘hat points’. Doing the ‘right thing’, such as sending compromising data to the authorities, provides you with White Hat points, while more selfish actions, such as sending funds to your own account, reward Black Hat points instead. As you move towards a certain direction on the game’s morality scale, you’ll receive differing benefits depending on the Hat Points you earn. While we’re not sure how much this affects the outcome of the story, this morality scale (and the associated reputation) does make Midnight Protocol feel more realistic and less like the game is railroading you towards a specific goal.
Conclusion
We were pleasantly surprised with Midnight Protocol. The unique spin on gameplay and the immersive storytelling emulated the feeling that we were a hacker. Although the game has a few early game balance issues, mostly because you’re “wasting” actions, our overall experience with Midnight Protocol was very positive. It’s a niche title, but if you’re in the specific niche that this game caters to, there is a good chance you’ll end up loving it.
Midnight Protocol - Review,







No Comments